In today’s complex digital landscape, achieving and maintaining compliance with standards like ISO 27001 or SOC 2 is not just a regulatory hurdle—it’s a critical foundation for trust and security. Endpoints, ranging from laptops and desktops to servers, are often the most vulnerable entry points and require meticulous attention to detail. Historically, this has meant juggling multiple tools, endless spreadsheets, and a reactive approach to compliance issues.
But what if there was a better way? A way to consolidate your endpoint monitoring, proactively identify compliance deviations, and even automate remediation, all from a single platform? Enter Anakage.
Contents
The Challenge: Endpoint Compliance is Fragmented and Resource-Intensive
Organizations often find themselves using a patchwork of solutions to manage endpoint compliance:
- Separate Monitoring Tools: One tool for log analysis, another for service status, a third for registry changes. This often means juggling applications like SolarWinds’ Server Configuration Monitor for registry changes, a standalone log management tool like Splunk or ManageEngine’s EventLog Analyzer for event logs, and a service monitoring tool like Nagios or Zabbix.
- Patch Management Tools: Separate systems like Microsoft SCCM or WSUS are needed just to track and deploy patches. This creates a siloed approach where patch status isn’t directly linked to compliance dashboards.
- Manual Audits: Tedious and error-prone manual checks of configurations and settings.
- Reactive Remediation: Discovering compliance gaps during an audit, leading to last-minute fire drills.
- Lack of Centralized Visibility: No single dashboard to provide a holistic view of endpoint health and compliance posture.
This fragmentation not only eats up valuable IT and security team resources but also increases the risk of overlooking critical compliance requirements.
Anakage: Your Integrated Solution for Endpoint Compliance
Anakage is designed to simplify and strengthen your endpoint compliance strategy by acting as a central hub for monitoring, analysis, and remediation. It brings together disparate monitoring needs under one roof, providing a “single pane of glass” for your ISO/SOC2 or other compliance-related endpoint controls. It helps you to monitor, generate audit ready reports from dashboards, remediate all in single tool.
1. Comprehensive Monitoring Capabilities
Anakage replaces the need for multiple, specialized tools by offering a robust suite of monitoring capabilities. It can effectively replace the functions of a range of tools, allowing you to track everything from a single console. You can effectively track:
- Essential Scripts: Ensure critical security scripts are running as expected.
- Registry Settings: Monitor for unauthorized or non-compliant changes to the Windows Registry, a function that would otherwise require a specialized tool like SolarWinds SCM.
- Event Logs: Keep a close eye on security-related events, login attempts, and system activities. This eliminates the need for separate log management and SIEM (Security Information and Event Management) tools like Splunk or EventLog Analyzer for endpoint logs.
- Applications: Track installed applications, versions, and identify unauthorized software.
- Services: Monitor the status of essential services, ensuring security and operational services are always running. This can replace the need for dedicated service monitors like Nagios or Zabbix for these specific compliance checks.
- Patch Management: Anakage eliminates the need for a separate patch management tool. It can monitor the patch status of all endpoints and report on missing security patches, a core requirement for compliance.
This comprehensive approach means you capture all the necessary data points required for stringent compliance frameworks.
2. The Anakage Compliance Dashboard: A Direct Link to Your Controls
One of Anakage’s most powerful features is its compliance dashboard. This intuitive interface provides:
- Pre-defined Controls: The dashboard can be configured to display controls directly relevant to ISO 27001, SOC 2, HIPAA, PCI DSS, or your organization’s specific policies. Anakage can monitor a wide array of endpoint-related controls, including:Key ISO 27001 Controls (Annex A)
- A.8.1 User Endpoint Devices: Monitoring for the secure configuration and use of laptops, desktops, and mobile devices.
- A.8.7 Protection Against Malware: Ensuring antivirus/anti-malware software is installed, running, and updated.
- A.8.9 Configuration Management: Verifying that security-critical configurations (e.g., firewall settings, secure boot) are in place.
- A.8.12 Data Leakage Prevention: Monitoring for unauthorized data transfers from endpoints.
- A.8.15 Logging: Ensuring all relevant security-related events are being logged and retained.
- A.8.16 Monitoring Activities: Continuously monitoring for anomalous behavior and security events on endpoints.
- A.8.19 Installation of Software on Operational Systems: Restricting and monitoring the installation of unauthorized software.
- A.7.7 Clear Desk and Clear Screen Policy: Automating screen locking after inactivity.
Key SOC 2 Controls (Common Criteria)
- CC6.1 – Logical Access: Ensuring that access to systems and data is restricted to authorized users. This includes monitoring for unauthorized access attempts and privilege escalation.
- CC6.2 – System Access: Verifying that user access is based on the principle of least privilege. Anakage can monitor for excessive user rights and permissions.
- CC7.1 – System Monitoring: Continuously monitoring system components (applications, services, logs) for security events.
- CC7.2 – Incident Response: Providing the capability to trigger automated remediation actions in response to a detected incident (e.g., a malware outbreak).
- CC7.4 – System Hardening: Verifying that endpoint configurations align with security baselines (e.g., disabling unnecessary services, hardening the OS).
- CC8.1 – Change Management: Monitoring for unauthorized or undocumented changes to endpoint configurations, services, or registry settings.
- CC9.1 – Risk Mitigation: Identifying and reporting on the status of controls designed to mitigate risks on endpoints.
- Real-time Status: Get an instant overview of your endpoint compliance posture. See at a glance which controls are compliant, non-compliant, or require attention.
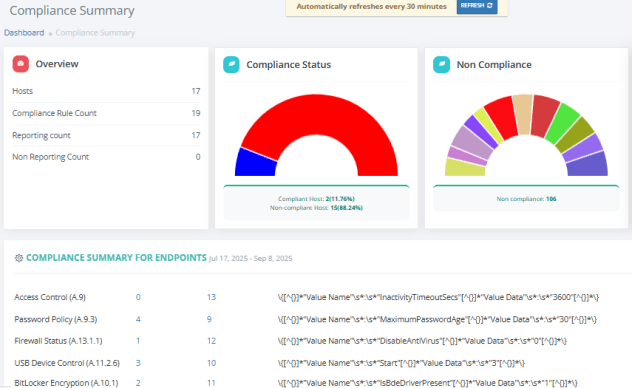
- Drill-down Capabilities: Easily dive into specific controls to understand the underlying issues, affected endpoints, and historical trends.
- Audit Trail: Maintain a clear record of all monitoring activities, changes, and remediation efforts, making audit preparation significantly smoother.
3. Proactive Remediation with Trigger Rules
Monitoring is only half the battle. The real power lies in taking action. Anakage empowers you with intelligent trigger rules:
- Automated Alerts: Set up alerts to notify your team immediately when a compliance deviation is detected (e.g., a critical service stops, an unauthorized registry change occurs).
- Automated Remediation: This is where Anakage truly shines. Instead of manual intervention, you can define trigger rules that automatically initiate remediation actions. For example:
- If a specific security service stops, Anakage can automatically restart it.
- If an unauthorized application is detected, it can trigger a script to uninstall it.
- If a critical registry setting is altered, Anakage can revert it to the compliant state.
- For patch management: Anakage can detect missing security patches and automatically trigger scripts or commands to install them, eliminating the need for a separate patch deployment system.
This proactive and automated approach not only saves time but drastically reduces your mean time to recovery (MTTR) for compliance issues, ensuring your endpoints remain secure and compliant around the clock.
The Anakage Advantage: Why It Matters for Your Organization
- Reduced Complexity: Consolidate multiple tools into one, simplifying your security stack.
- Enhanced Visibility: Gain a complete, real-time understanding of your endpoint compliance posture.
- Proactive Security: Move from reactive firefighting to proactive identification and automated resolution of issues.
- Audit Readiness: Streamline audit preparation with comprehensive data and clear reporting.
- Cost Savings: Optimize resource allocation by automating routine tasks and reducing manual effort.
- Improved Security Posture: By ensuring continuous compliance, you inherently strengthen your overall security.
Ready to Transform Your Endpoint Compliance?
Stop struggling with fragmented tools and manual processes. Anakage offers a powerful, integrated solution to meet the demands of modern compliance frameworks. Take control of your endpoints, simplify your audits, and build a truly resilient security posture.
Watch our latest video on “Revolutionizing IT Support: Tools Consolidation, Audit Readiness & Automated Remediation” here:

